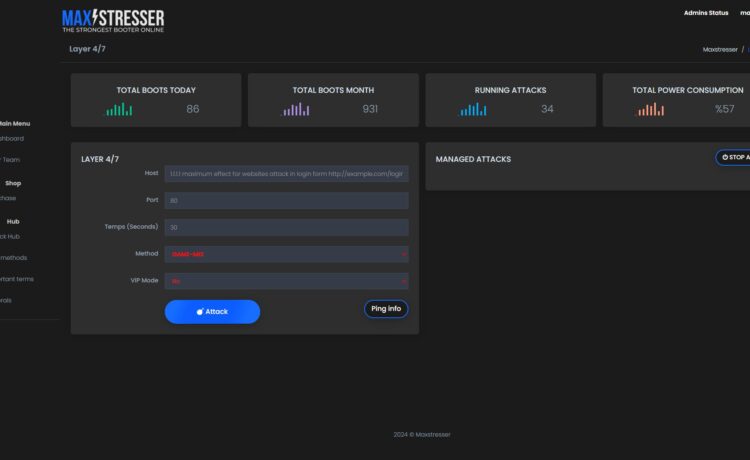
The financial incentives behind these IP stresser and booter operations are a driving force behind their proliferation. Cybercriminals easily monetize their illicit activities by offering “stresser” or “booter” services to other individuals or groups, charging a fee based on the duration and intensity of the attack. These services are often advertised on various dark web marketplaces, forums, and, sometimes, on Clearnet. The pricing model ranges from a few dollars for a basic attack to hundreds or thousands for a more sophisticated and prolonged assault.
Devastating impact on victims
A successful IP stresser or booter attack can devastate businesses and individual users. Targeted websites and online services are rendered inaccessible, leading to significant financial losses, reputational damage, and disruptions to critical operations. These attacks have been used to extort money from victims, with cyber criminals demanding payment in exchange for ceasing the assault. Failure to comply in the continuation or even escalation of the attack further compounded the harm.
Countering the threat- Ongoing efforts and challenges
The fundamental strategy has been to target the operators and administrators of these booter panels, seeking to identify and apprehend the individuals responsible. This has led to several high-profile arrests and takedowns of some of the most notorious IP stresser and booter services. However, the decentralized and adaptable nature of these operations presents significant challenges. As soon as one service is disrupted, new ones often emerge to fill the void, with operators leveraging the anonymity and accessibility of the dark web to continue their activities.
Ongoing efforts and strategies
A multifaceted approach is required to combat the threat of IP stresser and booter services, involving collaboration between law enforcement, cybersecurity experts, and the broader internet community.
1. Targeted enforcement and prosecution
Law enforcement agencies are intensifying their efforts to identify and apprehend the operators of these illicit services, leveraging advanced investigative techniques and international cooperation Visit darkvr.io for more info about IP Booter.
Successful prosecutions and severe penalties for those involved in creating, operating, and using IP stresser and booter services act as a deterrent and disrupt the criminal ecosystem.
2. Disruption and takedown of booter panels
Cybersecurity researchers and tech companies work to identify and track the infrastructure behind these booter panels, to disrupt their operations and take them offline.
This may involve techniques such as infiltrating the panels, identifying and shutting down hosting providers, and disrupting the payment mechanisms used by the operators.
3. Enhancing network security and resilience
Businesses and individuals are encouraged to implement robust network security measures, such as DDoS mitigation solutions, to better defend against the impact of IP stresser and booter attacks.
Ongoing investment in network infrastructure, threat intelligence, and incident response planning organizations maintain business continuity in the face of these attacks.
4. Awareness and education campaigns
Public awareness campaigns highlighting the dangers and consequences of using IP stresser and booter services deter potential users and reduce the overall demand for these illicit services.
Educating the public, especially young people, about the legal and ethical implications of such activities prevent the next generation of cybercriminals from engaging in these practices.
5. International collaboration and information sharing
Effective cooperation between law enforcement agencies, cybersecurity organizations, and internet service providers across different jurisdictions is crucial in disrupting the global networks behind IP stresser and booter operations.
Sharing of intelligence, best practices, and coordinated enforcement actions can enhance the overall effectiveness of the fight against these threats.